Global Security Environment
Expertise
Divisions
Special Programs
Centers
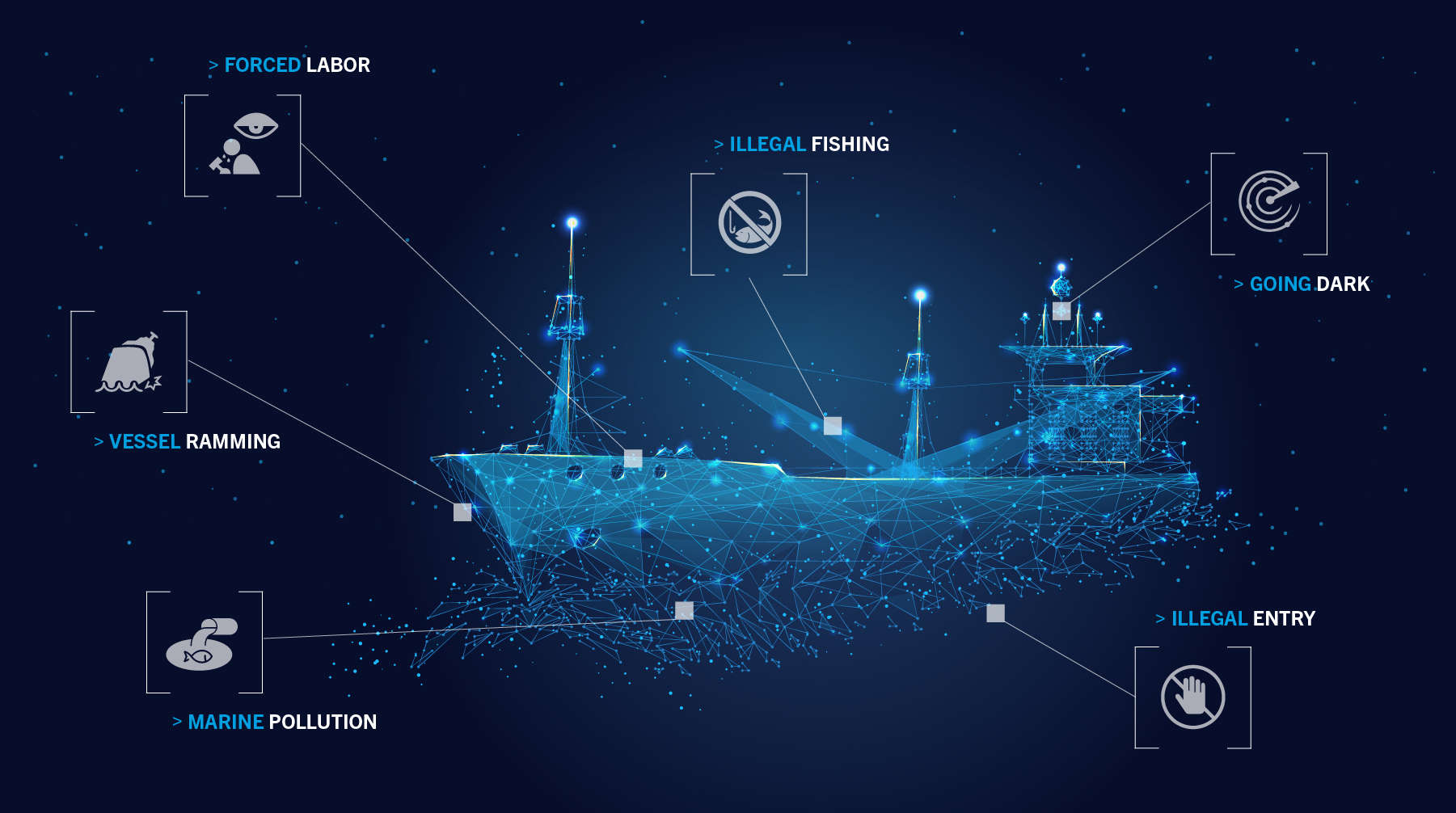
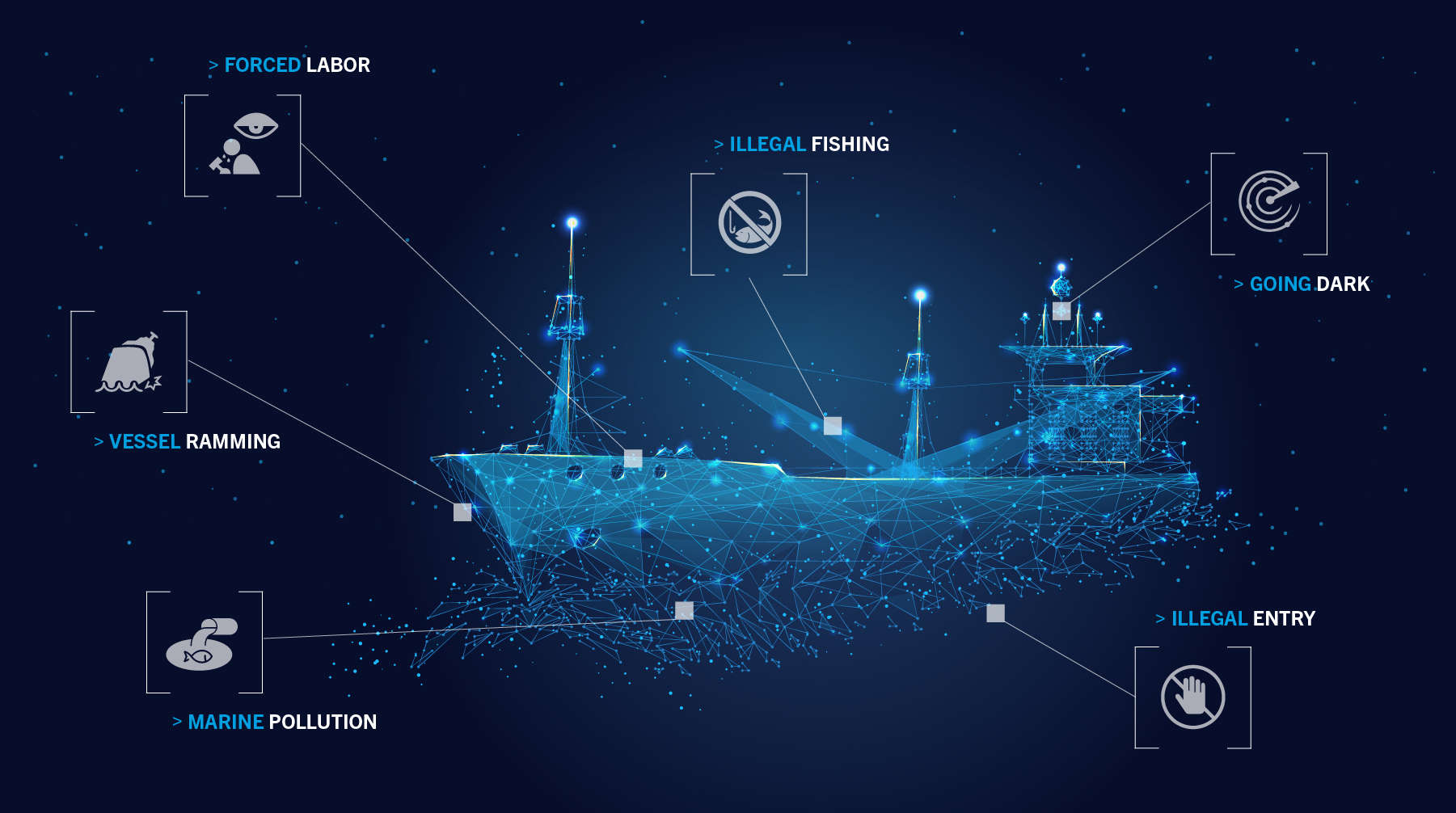
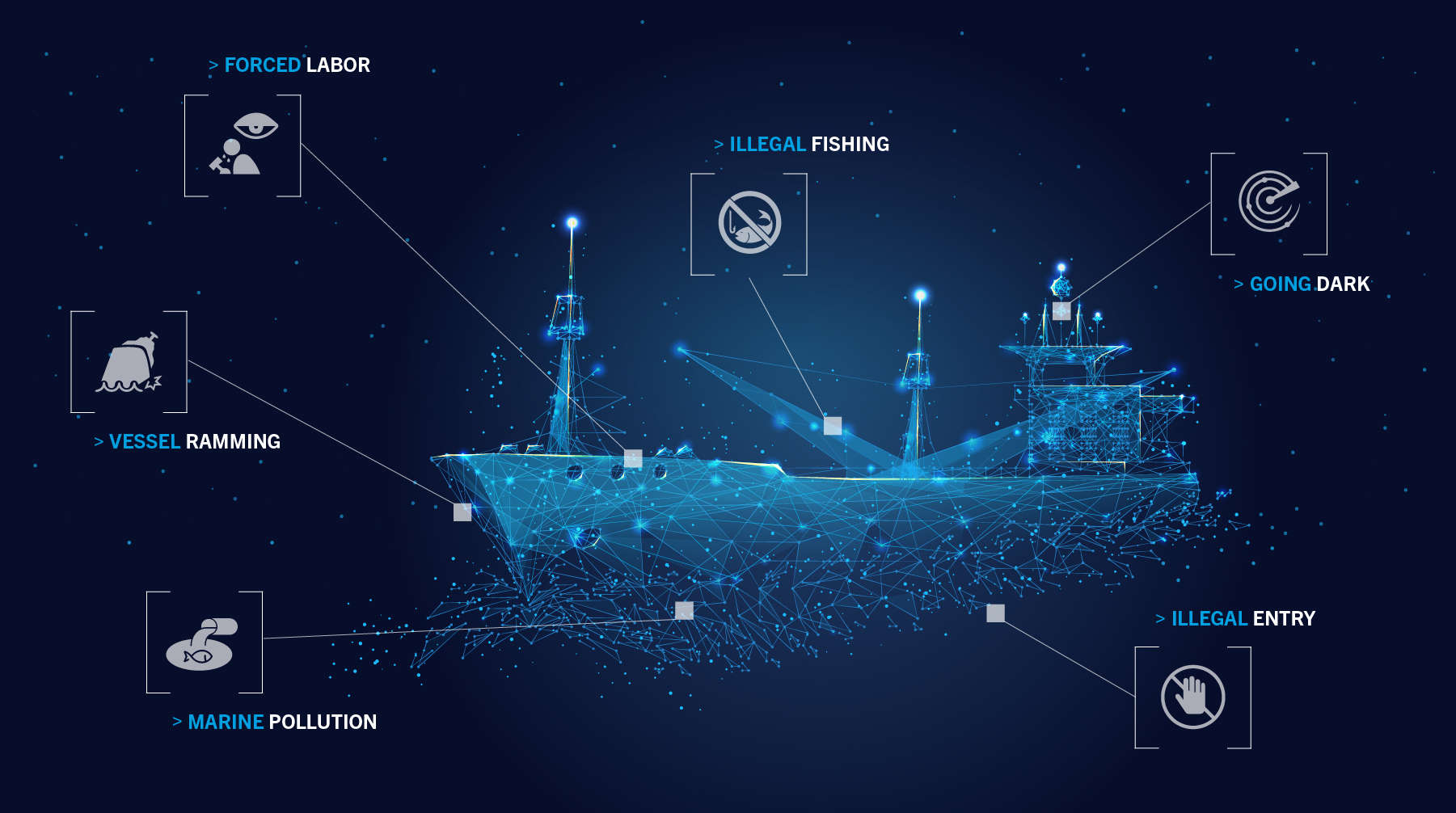
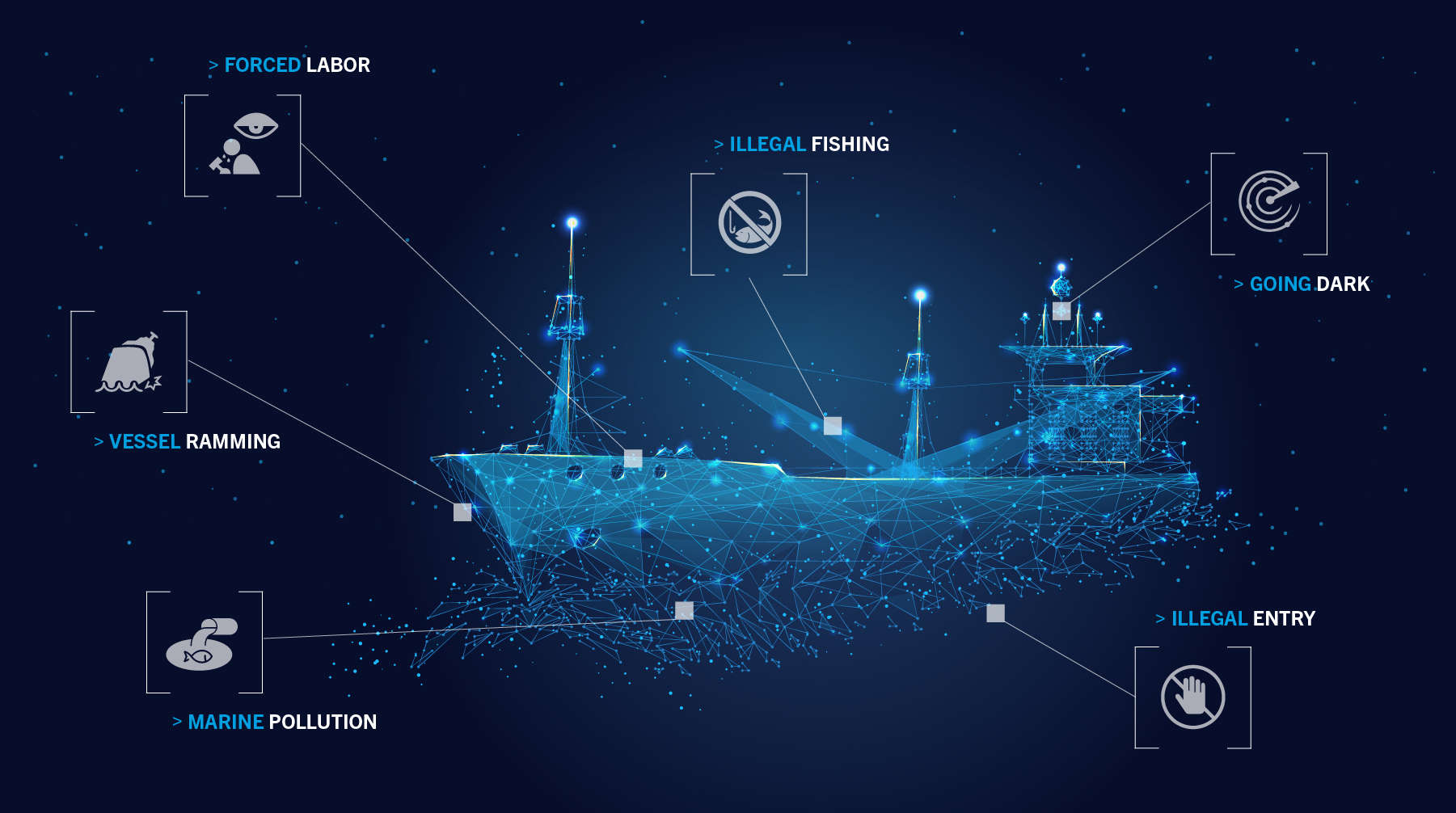
Illegal Entering and Anchoring in Malaysia’s Territorial Waters
Tampering with Automatic Identification Systems
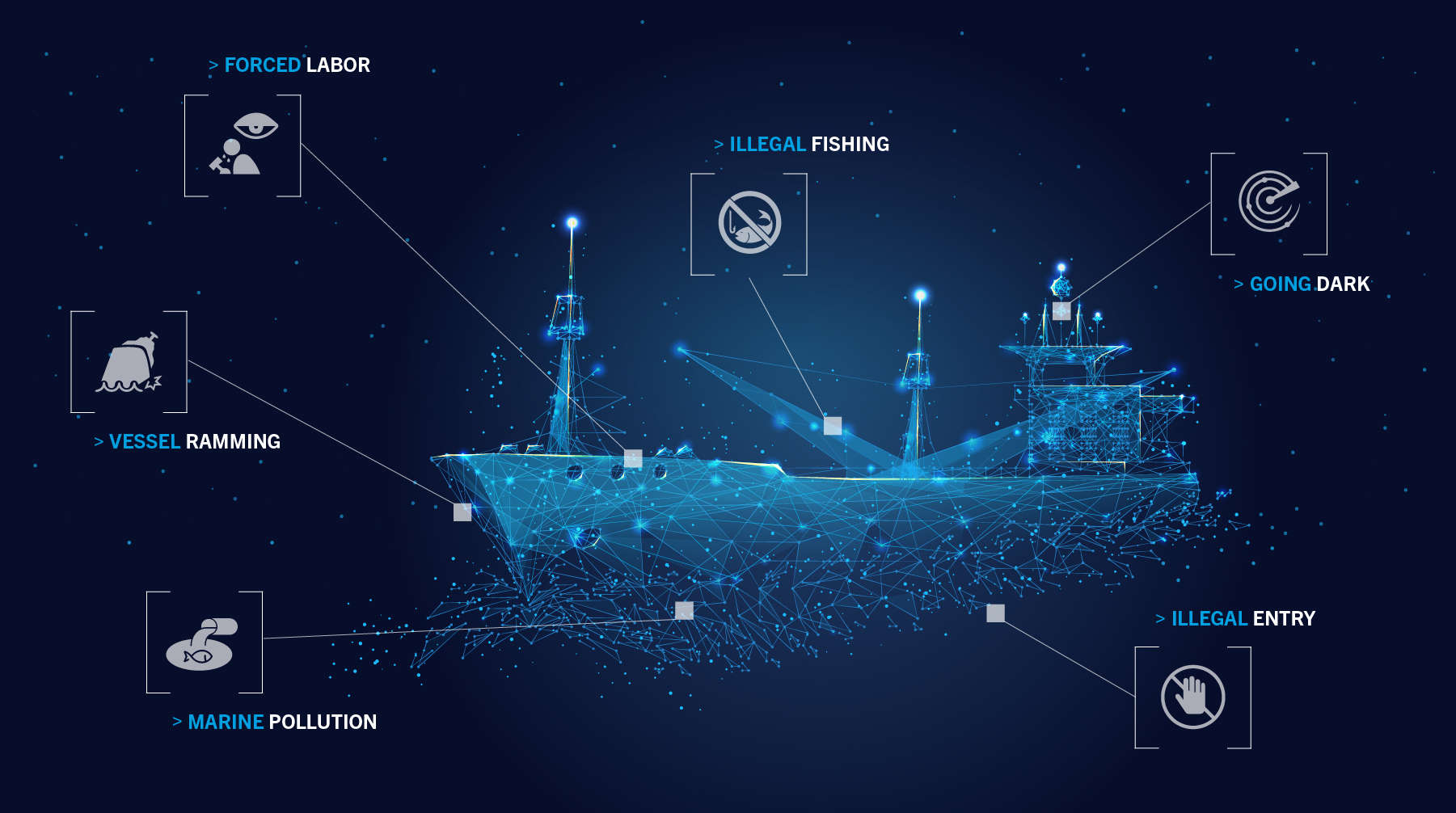
PRC Vessels Allegedly Ramming Foreign Fishing Vessels
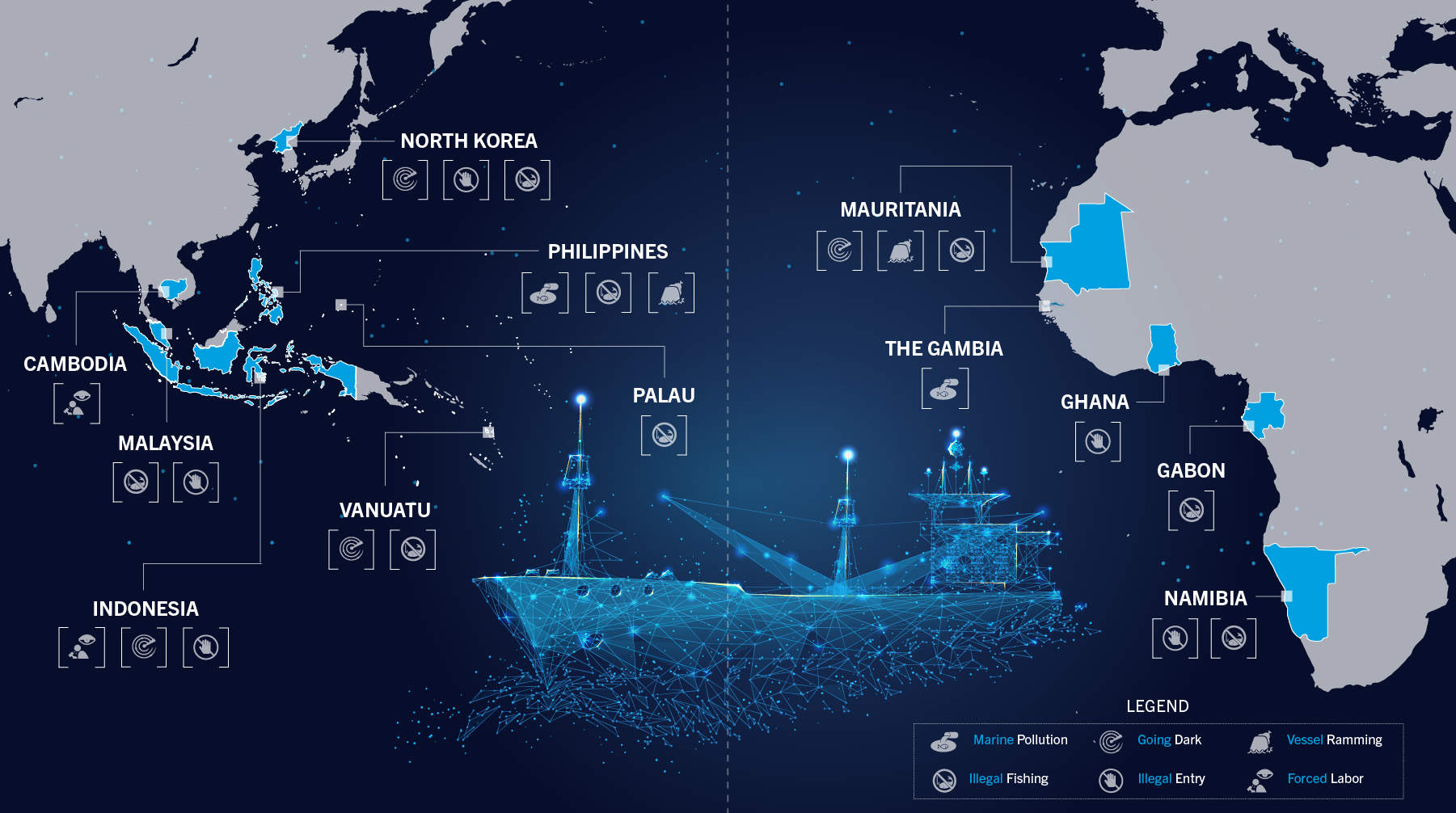
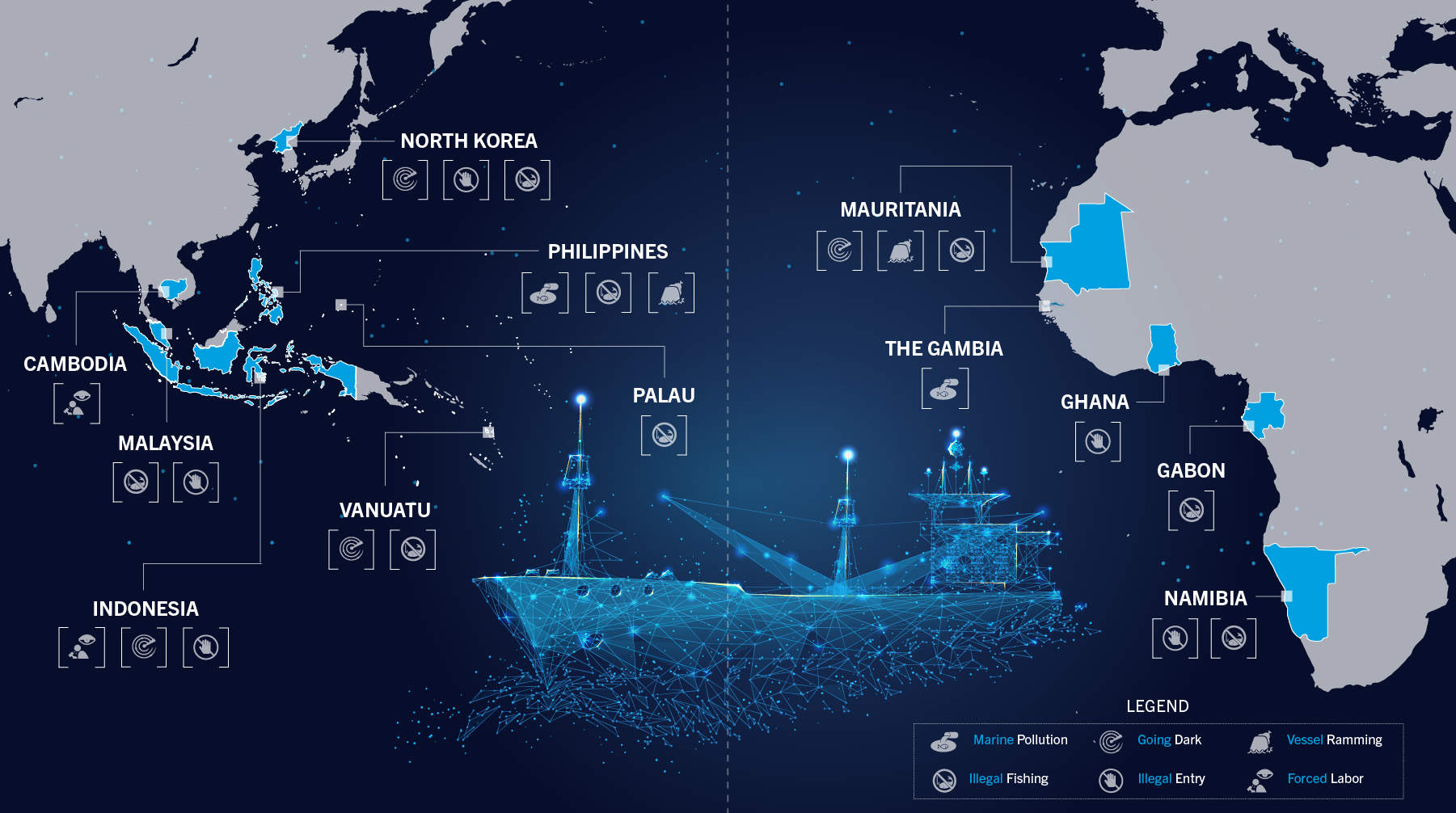
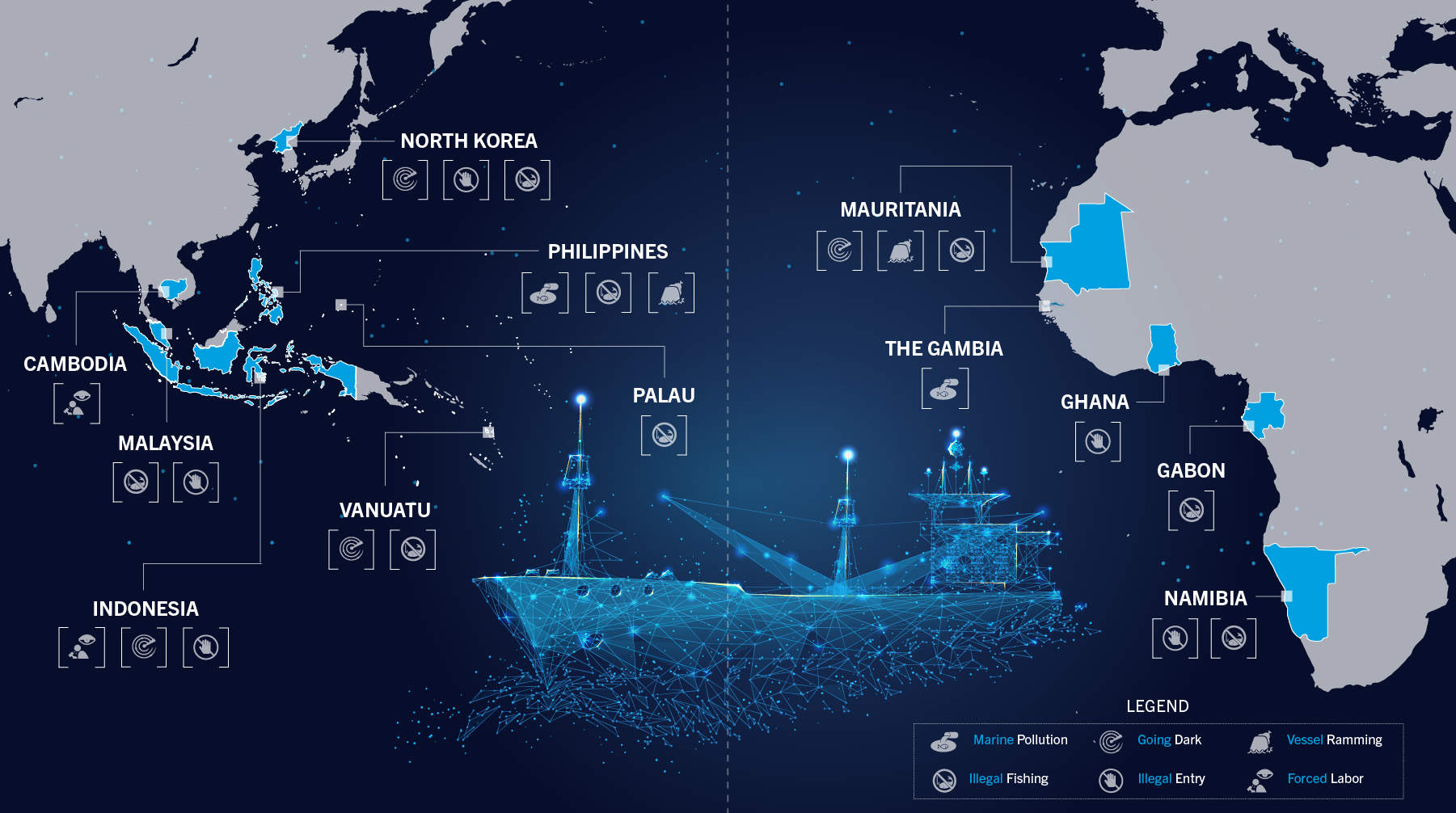
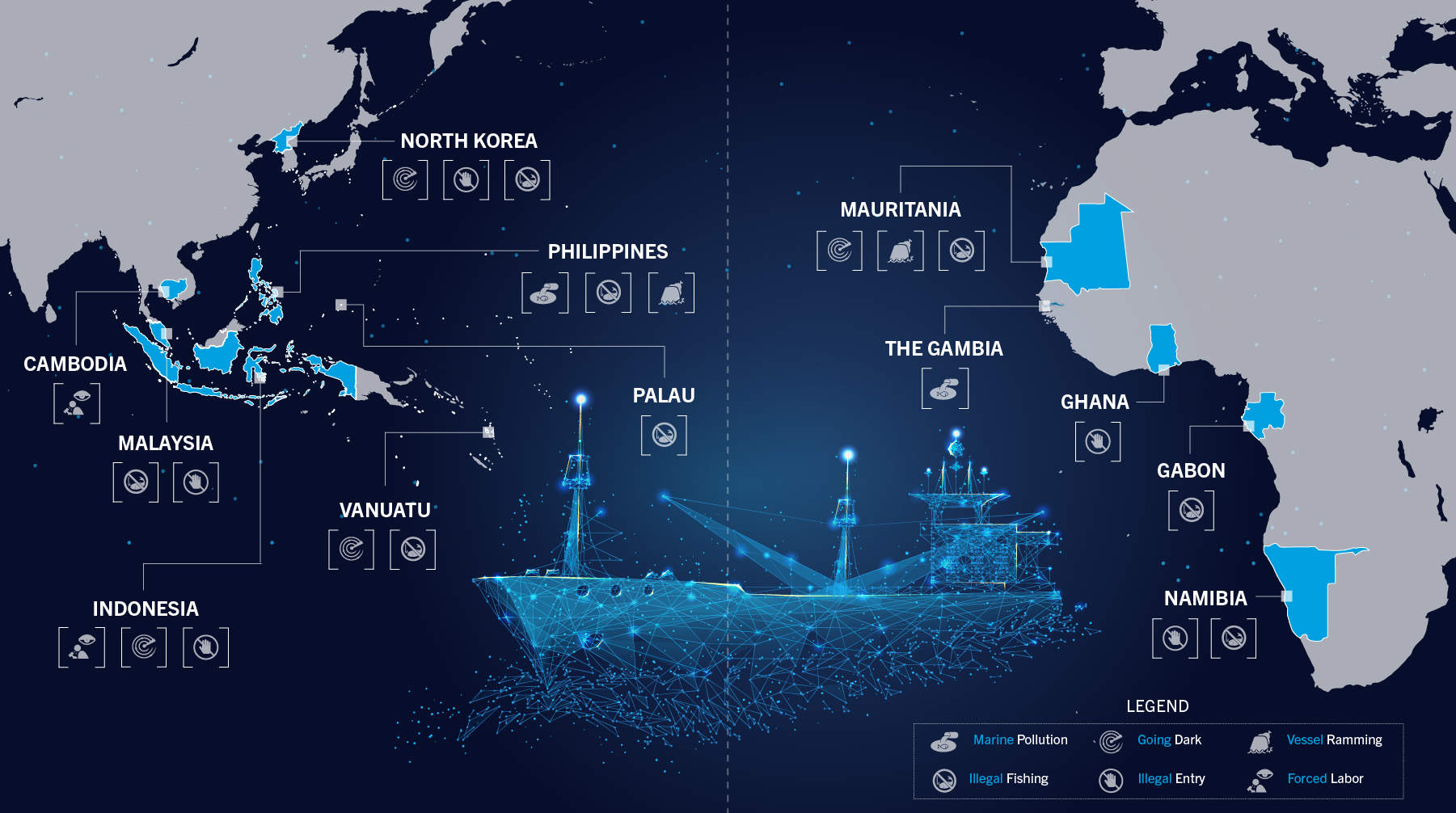
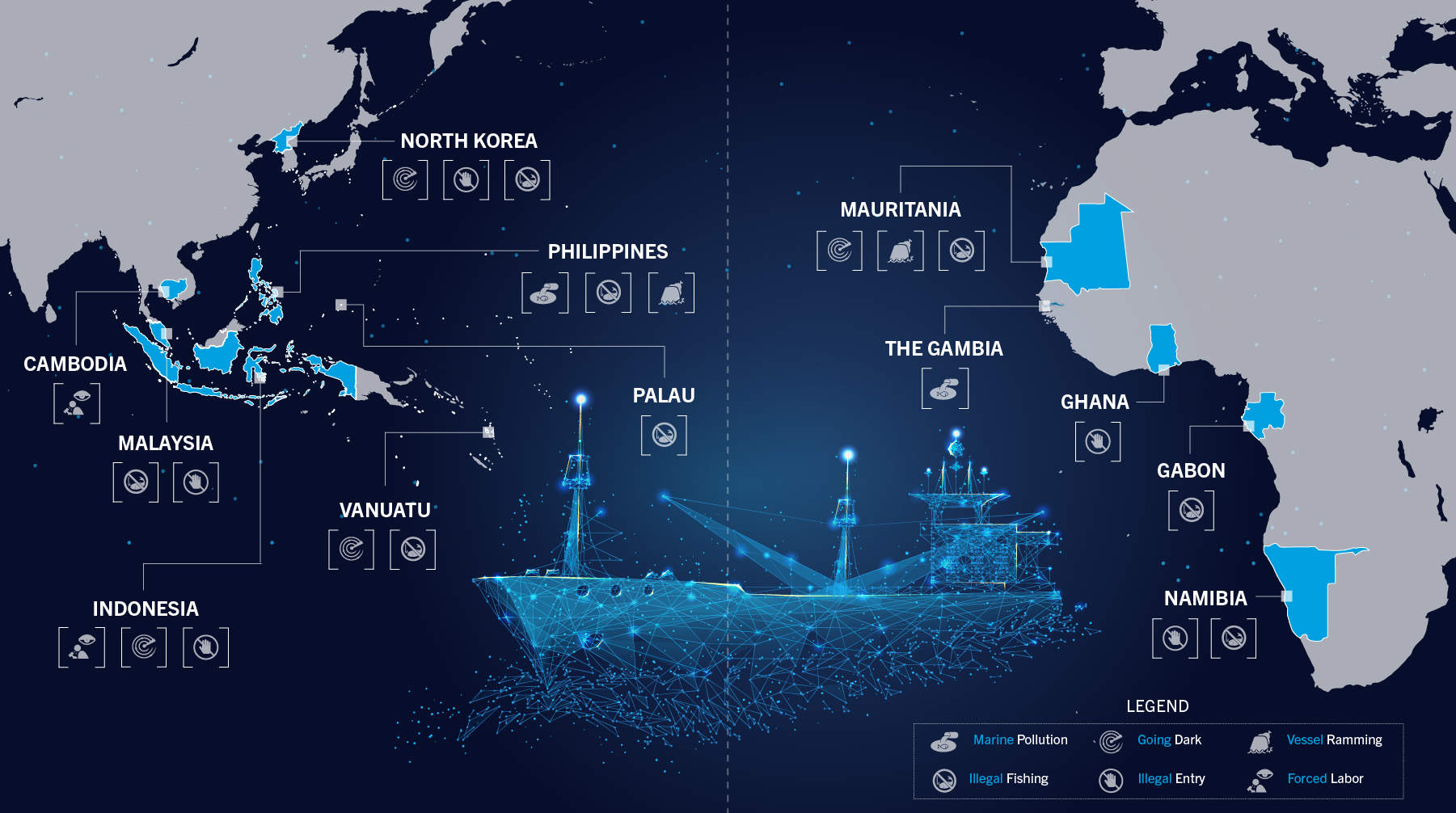
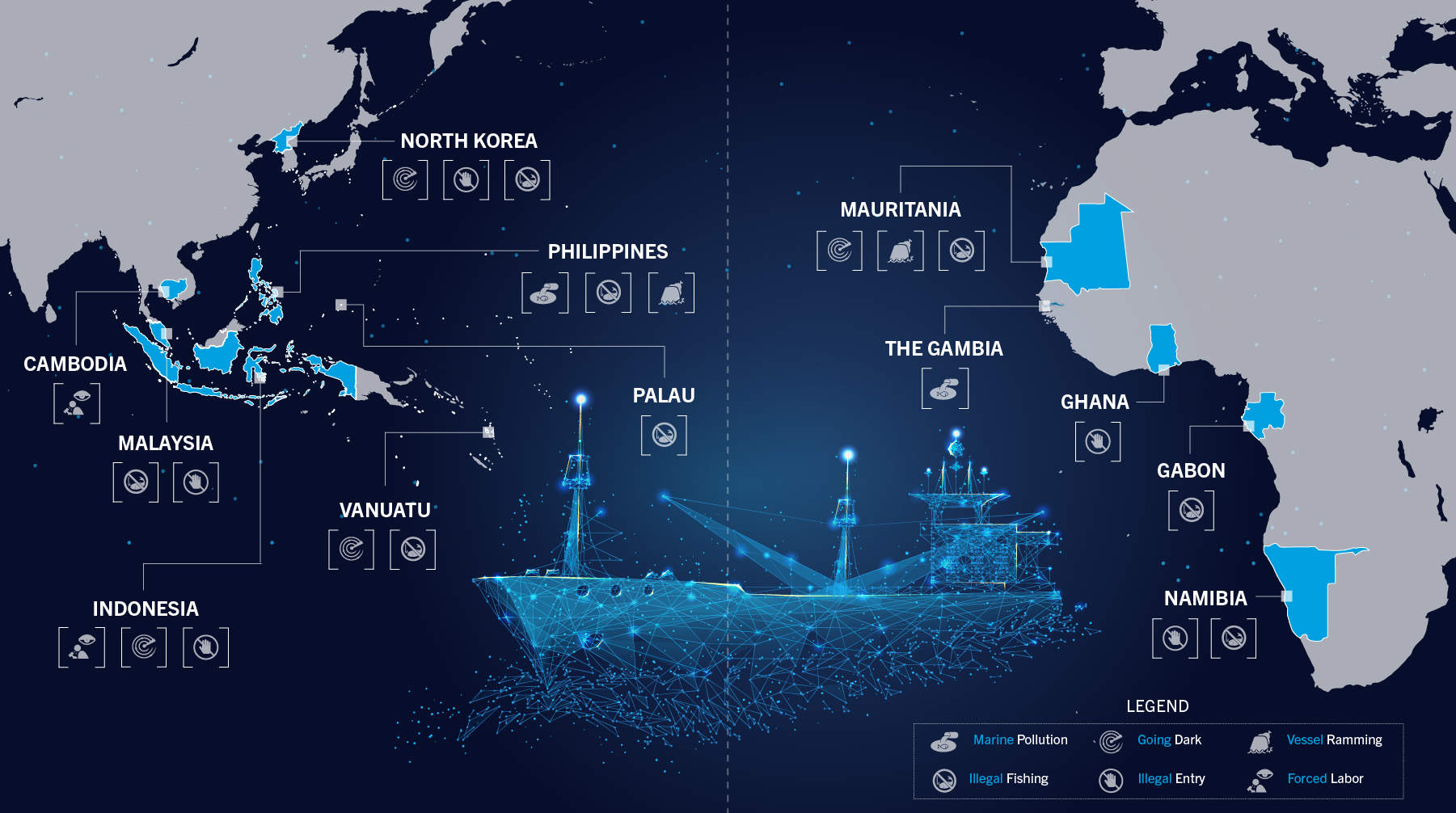
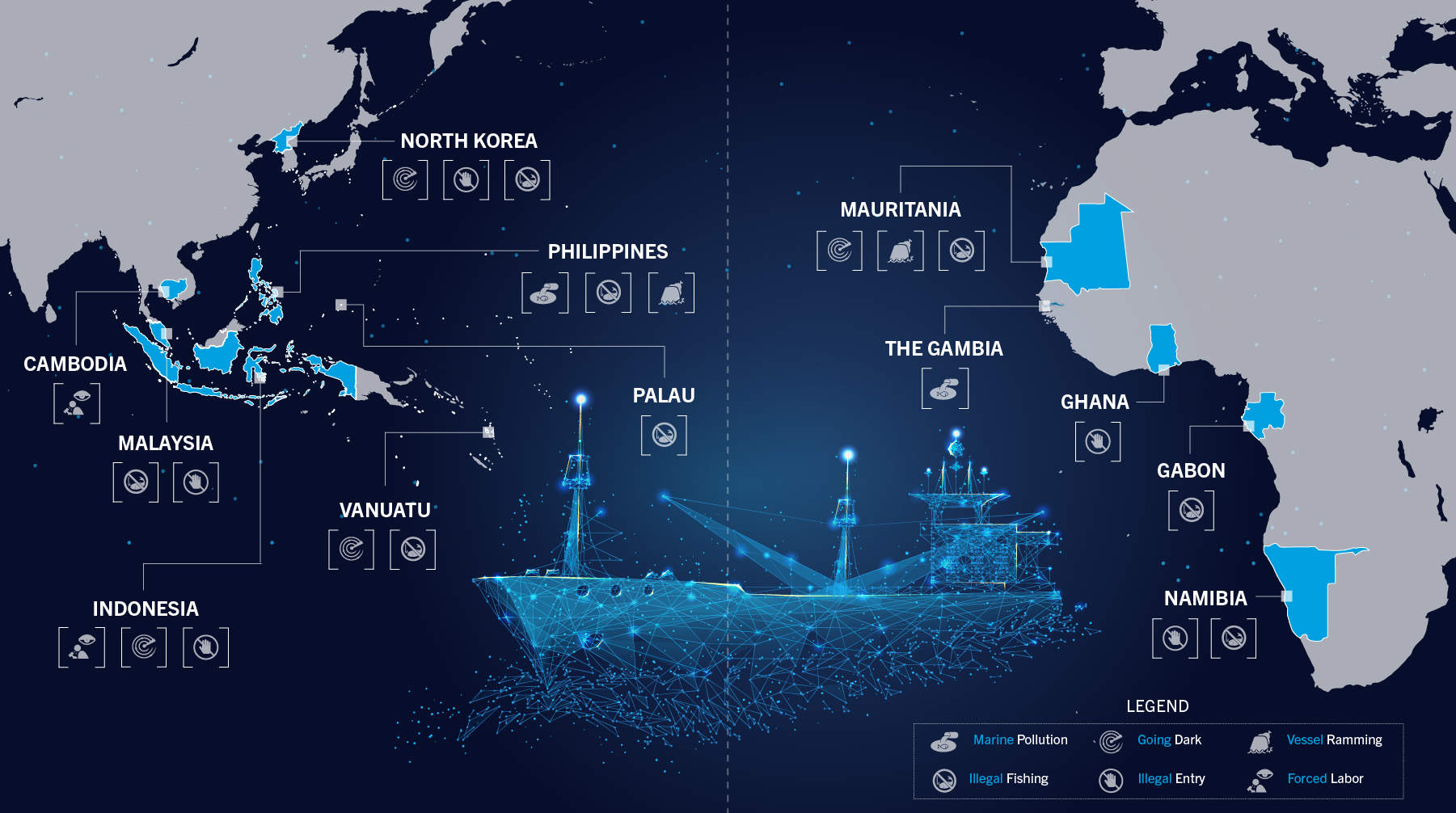
Exposing the Gap Between PRC Rhetoric and Illicit Maritime Activity: Case Study Compilation
Exposing the Gap Between PRC Rhetoric and Illicit Maritime Activity: Summary Report
Exposing the Gap Between PRC Rhetoric and Illicit Maritime Activity: Key Findings
Exposing the Gap Between PRC Rhetoric and Illicit Maritime Activity: Key Findings in Translation
Exposing the Gap Between PRC Rhetoric and Illicit Maritime Activity: Summary Report Tagalog Translation
PRC Trawler in Mauritania Restricted Area Rams Local Boat
PRC Nationals Smuggled into Cambodia by Sea
Harvesting Giant Clams in Philippine-Administered Waters
PRC Vessels Detained for Illegal Fishing in Vanuatu EEZ
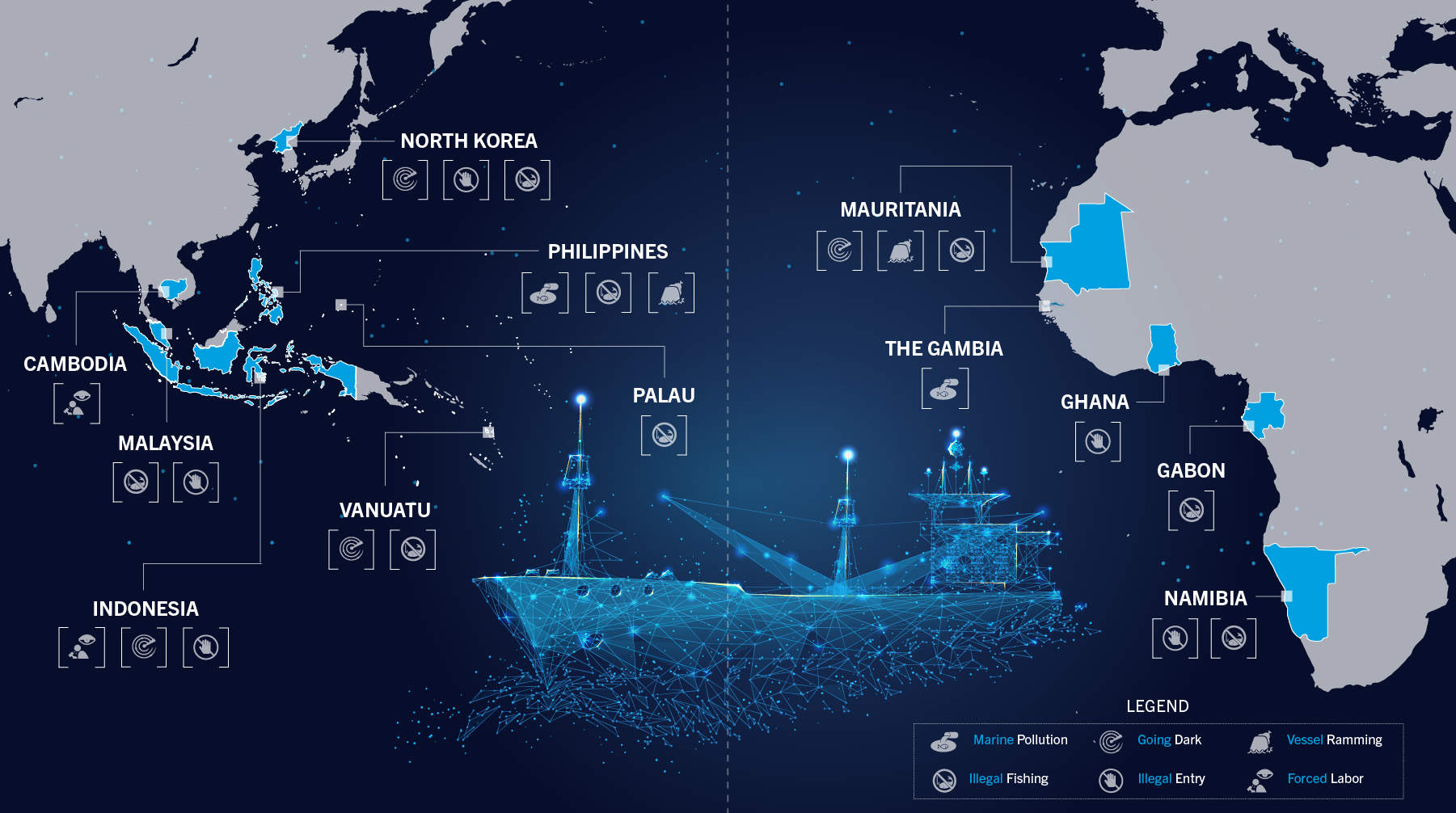
PRC Vessels Engaging in Illegal Fishing in Gabon

Implications of the U.S. Withdrawal from Afghanistan

North Korea: A Case Study of Asymmetric Relations

NATO Ally Contributions to the Space Domain
North Korea’s Arena of Asymmetric Advantage: Why We Should Prepare for a Crisis in the Yellow Sea

Maritime Sabotage: Lessons Learned and Implications for Strategic Competition

The AUKUS Submarine Agreement

China’s Efforts to Shape the Information Environment in the Mekong Region
Learning from the Past: US Domestic Counterterrorism from 1970 to 1985
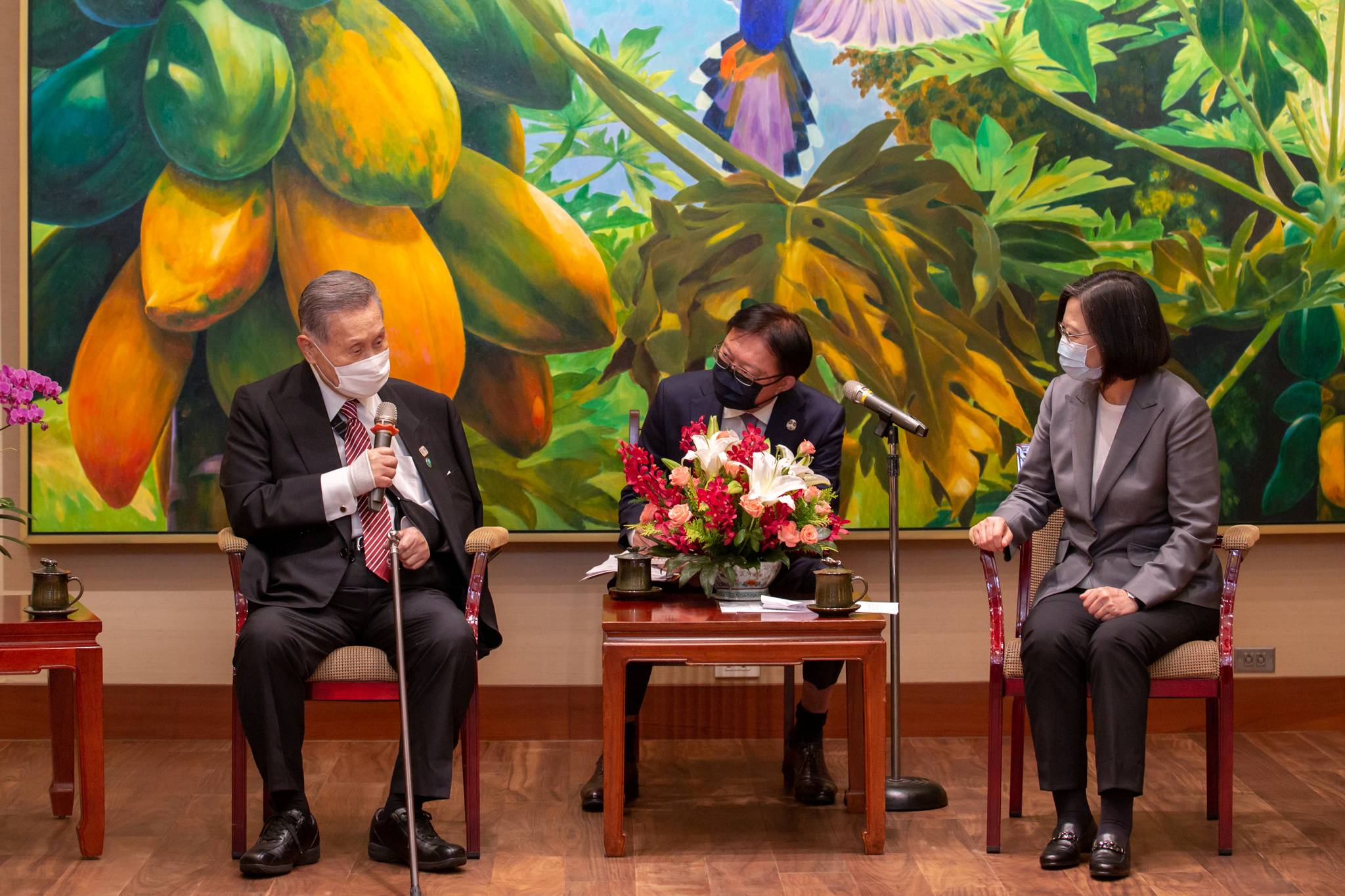
Japan Elevates Security Concerns Over Taiwan Strait
From UFO to UAP
6 Ways the U.S. Can Counter Extremist Groups in the COVID-19 Era
Why Pandemics Are National Security Threats